Use RedPhone to Encrypt Cell Phone Calls

"Hey, man, listen very carefully, man. Don't answer the phone, man. You got that? Don't answer the phone, even if its me calling, man, don't answer it, because I think the phone is bugged, man..."
- Pedro... I mean... Freddy
It's finally safe to answer the phone. Phone conversations are very difficult to keep private. You should never actually commit crimes, but if you joke about committing crimes over the phone, someone may be listening and they could use your jokes to convict you.
RedPhone Encrypts Cell Phone Calls
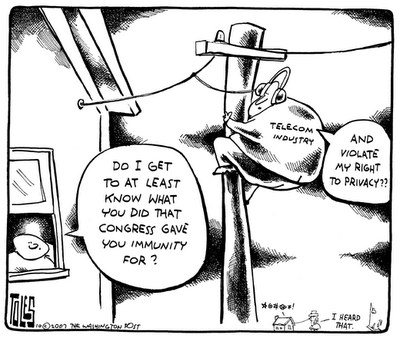
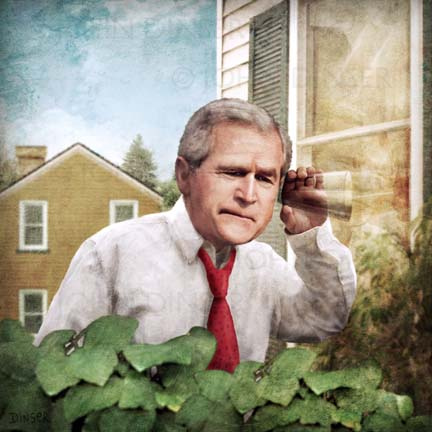
Telecom infrastructure is built so that the telecom companies can have secret access to all of your phone conversations. These same companies help law enforcement tap land lines and cell phones to spy on ordinary citizens without warrants or probable cause. Now you can use RedPhone to encrypt cell phone calls and protect your privacy.

When there is no neutral third party monitoring the use of phone taps by law enforcement, and when the service providers we use are complicit, the likelihood of abuse of law abiding citizens skyrockets, especially since the eavesdropping law enforcement officer might be involved in a criminal enterprise, be a stalker or a rapist. It is essential for honest people to protect their own private health information, communications with their attorney, trade secrets, negotiation strategies, embarrassing facts and keep stalkers from eavesdropping on conversations, no matter what kind of costume the the eavesdropper is wearing.
VoIP Is Better Than Traditional Phone Communication
To protect your phone calls from surreptitious surveillance without a warrant, the best option is to use VoIP services. VoIP is a way to make calls over the internet. Some of the most popular VoIP services are Skype and Google Voice.
There is one big weakness with using private VoIP services like Skype or Google Voice. They have the backdoor ability to let law enforcement secretly listen to your calls without a warrant. Open source VoIP can prevent the use of back doors by eavesdroppers but can be intimidating to use for computer novices.
RedPhone Protects Phone Privacy
RedPhone is a free program available for Android cell phones that lets you encrypt your cell phone calls to other RedPhone users. Your cell phone company can only see encrypted traffic, your ISP can only see encrypted traffic, and any other eavesdropper can only see encrypted traffic when you are encrypting your conversation on both ends with RedPhone.

Weaknesses of RedPhone
Although it is privately owned by Whisper Systems, they claim, unlike many other VoIP, that there is no backdoor ability for them or anyone else to secretly listen in on your conversations. They have yet to publish their source code to verify their claims, but they have indicated they might do so soon. RedPhone is also much more user friendly than most open source VoIP so novice users will find it very easy to use.
Text Messages Protected by TextSecure
Whisper Systems has also released a free program called TextSecure for Android phones which encrypts your text messages and stores them in an encrypted file on your phone. Even if your phone is searched, the text messages will remain encrypted. Text messages are a large part of the data that is routinely provided without a warrant to law enforcement. TextSecure can prevent warrantless disclosures of text message information to law enforcement.
These powerful tools are only available for Android phones right now. They are also still susceptible to breach if you have malware on your phone or your hardware has been compromised.
The Bigger Privacy Trend
The existence of tools like this represent a bigger trend in the empowerment of individuals over large institutions like government. Peaceful solutions, like many discussed in How To Vanish the book, that defend fundamental liberties against the encroachment of governments are being created faster than governments can stifle them. Even if some of these methods of protecting freedom are made illegal, it is less and less risky for people to use civil disobedience to fight unjust laws.

Conclusion
RedPhone and TextSecure are powerful tools to protect your privacy from corporate espionage, thieves, stalkers and other threats. They are free, simple and fun. Hopefully these kinds of solutions will be available on other cell phones soon. Don't forget to check out the complete strategies and tactics for protecting privacy in How To Vanish the book.
